9 Powerful Infrastructure as Code Security Guardrails (Prevent Cloud Misconfigurations Before Deployment)
Engineering leaders love Infrastructure-as-Code (IaC) because it’s repeatable, reviewable, and fast. Attackers love it for the same reason—one insecure Terraform module, Kubernetes manifest, or CloudFormation template can scale a misconfiguration across every environment.
That’s why infrastructure as code security can’t be a “best effort” checklist. It needs guardrails: policy-as-code controls that stop risky changes before they merge, plus continuous validation that detects drift and turns telemetry into incident-ready evidence.
In this guide, you’ll get copy-paste patterns for:
- Threat patterns in Terraform, Kubernetes, and CloudFormation
- Policy-as-code enforcement using OPA, Sentinel, and Checkov
- CI/CD merge gates that block insecure infrastructure pre-deploy
- Drift detection and continuous validation in production
- Telemetry linking infrastructure changes to incident response

For a more detailed guide on OAuth consent phishing prevention, malicious OAuth apps, and SaaS app governance, read How to Control OAuth App Sprawl Before Consent Phishing Becomes a SaaS Incident.
Why IaC security failures still cause major breaches
Most cloud incidents don’t start with “advanced exploitation.” They start with something boring:
- Public storage (buckets/containers)
- Overly permissive IAM (wildcards, admin roles)
- Open ingress rules (0.0.0.0/0 to sensitive ports)
- Kubernetes privileged workloads, host mounts, weak RBAC
- Disabled logging, missing encryption, missing egress controls
The root cause is consistent: the platform accepted a configuration that should never have been allowed.
So we’ll treat IaC like production code: tested, policy-checked, and merge-blocked when unsafe.
Threat patterns to watch (Terraform, K8s, CloudFormation)
Terraform threat patterns (common “fast breach” paths)
0.0.0.0/0on SSH/RDP/DB ports- IAM policies with
Action: "*"orResource: "*" - Unencrypted volumes / databases
- Missing audit logs (CloudTrail, flow logs, bucket access logs)
- Public access enabled on storage or load balancers
Kubernetes manifest threat patterns
privileged: truehostNetwork: true/hostPID: true- HostPath mounts to sensitive directories
- ServiceAccount tokens mounted broadly
- ClusterRoleBindings granting admin-like privileges
- Images not pinned (mutable tags)
CloudFormation threat patterns
- Public access configs (S3, security groups)
- Missing encryption-at-rest
- Missing logging and monitoring resources
- Broad IAM inline policies
The 9 Guardrails (copy-paste, merge-blocking)
Guardrail 1) Set secure IaC “defaults” (module contracts)
Before any tool runs, define what “secure by default” means in your Terraform modules and Helm charts:
- Require encryption (
kms_key_id,encrypted = true) - Require logging and metrics
- Require “deny public” defaults
- Require tags/labels for ownership, environment, and change tracking
Terraform example: enforce tags and encryption via module variables
variable "tags" {
type = map(string)
validation {
condition = contains(keys(var.tags), "owner") && contains(keys(var.tags), "env")
error_message = "tags must include: owner, env"
}
}
variable "kms_key_arn" {
type = string
description = "KMS key ARN required for encryption"
validation {
condition = length(var.kms_key_arn) > 20
error_message = "kms_key_arn is required"
}
}This is the foundation of terraform security best practices: make secure configurations the easiest path.
Guardrail 2) Run Checkov everywhere (dev + CI)
Static IaC scanning catches the “obvious” misconfigs early and cheaply.
Option A: Pre-commit hook (fast feedback)
.pre-commit-config.yaml
repos:
- repo: https://github.com/bridgecrewio/checkov
rev: "3.2.0"
hooks:
- id: checkov
args: ["-d", ".", "--quiet", "--compact"]Option B: CI gate (required check)
GitHub Actions: .github/workflows/iac-checkov.yml
name: iac-checkov
on:
pull_request:
paths:
- "**/*.tf"
- "**/*.yaml"
- "**/*.yml"
- "**/*.json"
jobs:
scan:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Run Checkov
uses: bridgecrewio/checkov-action@v12
with:
directory: .
quiet: true
compact: true
framework: terraform,kubernetes,cloudformationRule: if it fails in CI, it doesn’t merge. That’s how DevSecOps infrastructure guardrails work in practice.
Guardrail 3) Enforce Terraform policy-as-code with OPA (Conftest) on the PLAN
Static scanning is great, but policy-as-code cloud security becomes real when you gate on the Terraform plan JSON (what will actually change).
Generate plan JSON
terraform init
terraform plan -out tfplan.binary
terraform show -json tfplan.binary > tfplan.jsonConftest policy (OPA/Rego): block public SG rules + wildcard IAM
policy/terraform.rego
package terraform.guardrails
deny[msg] {
some r
r := input.resource_changes[_]
r.type == "aws_security_group_rule"
r.change.after.cidr_blocks[_] == "0.0.0.0/0"
port := r.change.after.from_port
port == 22 or port == 3389 or port == 5432
msg := sprintf("Blocked: public ingress (0.0.0.0/0) on sensitive port %v", [port])
}
deny[msg] {
some r
r := input.resource_changes[_]
r.type == "aws_iam_policy"
doc := r.change.after.policy
contains(doc, "\"Action\":\"*\"") # pragmatic string check
msg := "Blocked: IAM policy contains Action:\"*\" (use least privilege)"
}
deny[msg] {
some r
r := input.resource_changes[_]
r.type == "aws_iam_policy"
doc := r.change.after.policy
contains(doc, "\"Resource\":\"*\"")
msg := "Blocked: IAM policy contains Resource:\"*\" (scope resources)"
}Run Conftest in CI
conftest test tfplan.json -p policy/This model catches “hidden” risk even when the HCL looks innocent (because the plan reveals computed values).
Guardrail 4) Sentinel policy for Terraform Cloud/Enterprise (hard fail gates)
If you use Terraform Cloud/Enterprise, Sentinel gives first-class policy enforcement.
restrict-public-ingress.sentinel
import "tfplan/v2" as tfplan
main = rule {
all tfplan.resource_changes as rc {
not (
rc.type is "aws_security_group_rule" and
rc.change.actions contains "create" and
rc.change.after.cidr_blocks contains "0.0.0.0/0" and
(rc.change.after.from_port is 22 or rc.change.after.from_port is 3389)
)
}
}Policy posture options:
- advisory (warn) for week 1–2
- soft mandatory (can override with justification)
- hard mandatory (no override)
Start advisory → graduate to hard fail on the top 3 misconfigs you see.
Guardrail 5) Kubernetes admission control (OPA Gatekeeper) for manifest security
“Kubernetes configuration security” is often where the blast radius explodes. Admission control is how you stop unsafe pods before they exist.
ConstraintTemplate: block privileged containers
apiVersion: templates.gatekeeper.sh/v1
kind: ConstraintTemplate
metadata:
name: k8sblockprivileged
spec:
crd:
spec:
names:
kind: K8sBlockPrivileged
targets:
- target: admission.k8s.gatekeeper.sh
rego: |
package k8sblockprivileged
violation[{"msg": msg}] {
container := input.review.object.spec.containers[_]
container.securityContext.privileged == true
msg := "Blocked: privileged container is not allowed"
}Constraint: enable it cluster-wide
apiVersion: constraints.gatekeeper.sh/v1beta1
kind: K8sBlockPrivileged
metadata:
name: deny-privileged
spec:
match:
kinds:
- apiGroups: [""]
kinds: ["Pod"]Add similar constraints for:
- hostPath mounts
- hostNetwork/hostPID
- images using
:latest - ClusterRoleBindings to
cluster-admin
Guardrail 6) CloudFormation policy checks (OPA/Conftest) to stop public storage
If you have CloudFormation templates, you can apply the same policy-as-code approach.
Example deny rule for S3 public access configurations:policy/cfn.rego
package cfn.guardrails
deny[msg] {
some rname
r := input.Resources[rname]
r.Type == "AWS::S3::Bucket"
not r.Properties.PublicAccessBlockConfiguration.BlockPublicAcls
msg := sprintf("Blocked: S3 bucket %s missing BlockPublicAcls", [rname])
}Run it:
conftest test template.yaml -p policy/Guardrail 7) CI/CD enforcement: fail fast before merge (and make it standard)
The goal isn’t “scan.” The goal is: unsafe IaC can’t merge.
Recommended minimum gates for IaC PRs:
- Checkov (static)
- Conftest (policy)
- Formatting + validation (
terraform fmt,terraform validate) - Optional:
terraform planon PR (staging creds)
One workflow that does all three
name: iac-guardrails
on:
pull_request:
paths:
- "infra/**"
- "**/*.tf"
- "**/*.yaml"
- "**/*.yml"
- "**/*.json"
jobs:
guardrails:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Terraform fmt/validate
working-directory: infra
run: |
terraform fmt -check -recursive
terraform init -backend=false
terraform validate
- name: Checkov scan
uses: bridgecrewio/checkov-action@v12
with:
directory: infra
framework: terraform,kubernetes,cloudformation
quiet: true
compact: true
- name: OPA policy test (Conftest)
run: |
conftest test infra -p policy/Then make it a required status check in branch protection.
Guardrail 8) Drift detection + continuous validation in production
Even perfect CI can’t prevent drift caused by:
- emergency console changes
- hotfixes during incidents
- operator actions
- partial failures
Terraform drift check (safe “refresh-only”)
terraform init
terraform plan -refresh-only -detailed-exitcode
# exit code 2 = drift detectedRun daily (or per deploy) and route drift to:
- a ticket
- a Slack/Teams alert
- a “break glass” review if drift touches sensitive resources
Kubernetes drift check (GitOps style)
If you run GitOps (e.g., ArgoCD/Flux), drift becomes visible by default. If not, you can still run:
kubectl diff -f k8s/The key outcome: drift is not “a surprise during an incident.” It’s a tracked signal.
Guardrail 9) Link infrastructure telemetry to incident response
During an incident, “what changed?” is usually the first question. Make IaC changes traceable by design.
Tag resources with deployment metadata (Terraform)
locals {
common_tags = {
owner = "platform"
env = var.env
repo = "infra-repo"
git_sha = var.git_sha
change_id = var.change_id
}
}
resource "aws_s3_bucket" "logs" {
bucket = "org-${var.env}-logs"
tags = local.common_tags
}Kubernetes: add annotations/labels for change tracking
metadata:
labels:
app: payments
env: prod
annotations:
change.git_sha: "GIT_SHA_HERE"
change.pipeline: "github-actions"
change.owner: "platform"Now incident response can pivot quickly:
- from a suspicious cloud event → to the exact change → to the PR → to the reviewer → to the pipeline logs
That shortens containment time and improves post-incident evidence.
For deeper “evidence-ready” patterns, pair this with forensics-focused engineering guidance like Cyber Rely’s forensics-ready and observability controls.
Build a secure developer workflow (without slowing deployments)
A rollout that sticks usually follows this sequence:
- Week 1: Turn on Checkov in CI (non-blocking), measure top failures
- Week 2: Add 2–3 OPA/Sentinel rules for the highest-risk misconfigs
- Week 3: Make gates required for
infra/paths - Week 4: Add drift detection + tagging for incident traceability
This keeps engineering velocity while raising the floor on cloud misconfiguration prevention.
Where our Free Tool fits (validation + reporting)
IaC guardrails protect what you intend to deploy. A scanner helps validate what’s actually exposed.
Use the Free Website Vulnerability Scanner as a practical “outside-in” check—especially for:
- TLS posture
- security headers
- exposed panels and common misconfigurations
- high-signal web-facing issues that complement IaC findings
Free Website Vulnerability Scanner Tool Page
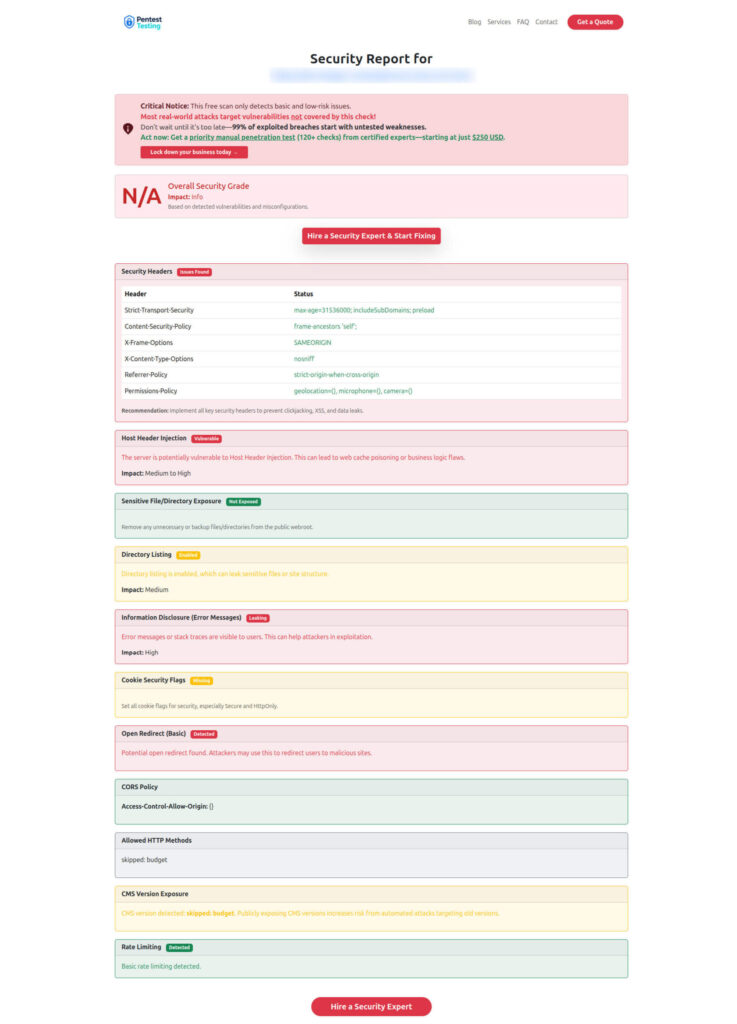
Sample Report to check Website Vulnerability
Try it here: https://free.pentesttesting.com/
When you need expert help (services)
If you want human-led validation (beyond automated CI rules), these services pair naturally with infrastructure as code security guardrails:
- Cyber Rely – API Penetration Testing Services: https://www.cybersrely.com/api-penetration-testing-services/
- Pentest Testing Corp – Risk Assessment Services: https://www.pentesttesting.com/risk-assessment-services/
- Pentest Testing Corp – Remediation Services: https://www.pentesttesting.com/remediation-services/
- Pentest Testing Corp – Digital Forensic Analysis Services: https://www.pentesttesting.com/digital-forensic-analysis-services/
Recent Cyber Rely reads (internal links)
If you’re building a broader “secure delivery” program, these recent Cyber Rely posts pair well with this guide:
- 9 Powerful Asynchronous System Security Fixes — https://www.cybersrely.com/asynchronous-system-security-secure-message/
- 7 Powerful Secure Deployments Guardrails (Forensics-Ready) — https://www.cybersrely.com/secure-deployments-guardrails-forensics-ready/
- 7 Powerful Secure Observability Pipeline Controls — https://www.cybersrely.com/secure-observability-pipeline/
- 7 Battle-Tested Feature Flag Security Controls — https://www.cybersrely.com/feature-flag-security-safe-canary-rollouts/
- 7 Powerful Ways Observability for Security Works — https://www.cybersrely.com/observability-for-security-telemetry-enrichment/
Also relevant (code-heavy CI patterns):
- 6 Powerful Security Chaos Experiments for CI/CD — https://www.cybersrely.com/security-chaos-experiments-for-ci-cd/
- 5 Proven CI Gates for API Security: OPA Rules You Can Ship — https://www.cybersrely.com/ci-gates-for-api-security/
Implementation checklist (copy/paste)
Minimum viable IaC security guardrails:
- Checkov in CI for Terraform/K8s/CloudFormation
- OPA/Conftest policy gate on Terraform plan JSON
- Kubernetes admission policies (privileged, hostPath, :latest)
- Branch protection: required checks for
infra/ - Drift detection pipeline (
terraform plan -refresh-only) - Change metadata tags/annotations for IR traceability
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about Infrastructure as Code Security Guardrails.