Session Token Security and Mismanagement: The Hidden Flaw Behind “Secure” SaaS Architectures
Authentication is not the finish line.
A lot of SaaS teams invest heavily in login security, SSO integrations, MFA, and identity providers, then leave the session layer under-designed. That is where many real incidents begin. Not at password entry. Not at the OAuth consent screen. After authentication succeeds.
That is why session token security deserves far more engineering attention than it usually gets.
A “secure” SaaS architecture can still fail if it issues reusable refresh tokens without reuse detection, never rotates session identifiers, stores browser tokens where JavaScript can read them, or has no reliable token revocation model when roles change, devices are lost, or suspicious activity appears. In practice, attackers often prefer stealing trust that already exists over breaking authentication from scratch.
This post complements authentication-focused discussions like consent abuse and redirect misuse by focusing on what happens next: how trust is created, extended, replayed, revoked, and destroyed inside the session layer.

Why attackers target sessions after login
Once an attacker holds a valid session cookie, access token, or refresh token, they are no longer fighting your login page. They are borrowing your application’s trust model.
That changes the problem completely.
Instead of brute forcing credentials, they can replay a token. Instead of bypassing MFA, they can ride the session established after MFA. Instead of exploiting a dramatic RCE, they can quietly keep access through long-lived refresh flows, weak logout handling, or missing revocation on role changes.
This is why session hijacking prevention is not a “nice-to-have” hardening layer. It is part of core application security design.
A few principles matter here:
- A JWT is a token format, not a session strategy.
- OAuth success does not mean your app-level session handling is secure.
- Short-lived access alone is not enough if refresh token security is weak.
- Logout is meaningless if old tokens still work.
- MFA value collapses if post-login sessions can be replayed without friction.
In modern SaaS, the real question is not only “Who authenticated?” It is also:
- What token was issued?
- Where is it stored?
- How long is it trusted?
- What invalidates it?
- What happens if it is replayed?
- What happens when user risk changes mid-session?
What session token security actually means
Good session token security covers the full lifecycle of trust:
- issuance
- storage
- validation
- rotation
- revocation
- expiration
- forensic visibility
If even one of those is weak, the rest of the system inherits that weakness.
That is why many SaaS auth flaws are really session flaws wearing an authentication label.
Common engineering mistakes that create SaaS auth flaws
1. Not rotating the session identifier at the right moments
If the same session identifier survives pre-login and post-login, you have created room for session fixation.
Rotation should happen at minimum:
- immediately after successful login
- after step-up authentication
- after privilege elevation
- after password reset or account recovery
- after suspicious-device revalidation flows
If you only rotate on initial login and nowhere else, elevated actions may still inherit stale trust.
Node/Express example: rotate on successful login
app.post("/login", async (req, res, next) => {
try {
const user = await authenticate(req.body.email, req.body.password);
req.session.regenerate((err) => {
if (err) return next(err);
req.session.userId = user.id;
req.session.role = user.role;
req.session.authnTime = Date.now();
req.session.tokenVersion = user.tokenVersion;
res.json({ ok: true });
});
} catch (err) {
next(err);
}
});And make sure your session cookie is configured intentionally:
app.use(
session({
name: "__Host-session",
secret: process.env.SESSION_SECRET,
resave: false,
saveUninitialized: false,
cookie: {
httpOnly: true,
secure: true,
sameSite: "lax",
path: "/",
maxAge: 1000 * 60 * 30
}
})
);For browser-based SaaS, the __Host- prefix plus Secure, HttpOnly, and a deliberate SameSite policy are usually better defaults than loose, legacy cookie settings.
2. Treating refresh tokens like passive plumbing
Refresh token security is where many otherwise mature systems fail.
Common mistakes include:
- no rotation on refresh
- no token family tracking
- no reuse detection
- very long refresh lifetimes
- storing raw refresh tokens server-side
- allowing multiple parallel refreshes with no conflict handling
- not killing the whole token family after reuse is detected
A stolen refresh token is often more valuable than a short-lived access token. If it can be replayed successfully, the attacker can keep rehydrating trust long after the original session should have died.
A better pattern is rotating refresh tokens with family tracking and server-side hashing.
Recommended refresh token model
auth_refresh_tokens
- jti
- family_id
- user_id
- session_id
- token_hash
- issued_at
- expires_at
- rotated_from_jti
- revoked_at
- reuse_detected
- device_label
- ip_first_seen
- ua_hashRotation logic
- Client submits refresh token A.
- Server hashes token A and verifies it matches an active record.
- Server marks A as rotated/revoked.
- Server creates token B in the same family.
- Server returns new access token + refresh token B.
- If token A is ever used again, mark the family compromised and revoke all descendants.
That is one of the most practical ways to stop silent replay.
3. Using JWTs without a revocation model
JWT misuse is still common because teams like the operational simplicity of stateless tokens, then discover the cost later.
Problems show up when:
- the token has no
jti - there is no
sid - there is no server-side session record
- the token lifetime is too long
- password reset does not invalidate old tokens
- privilege changes do not invalidate old tokens
- “logout all devices” has no reliable backend effect
If your answer to token revocation is “wait for expiry,” your design is probably too trusting for modern SaaS.
At minimum, JWT-backed systems should consider:
- short access token TTLs
jtiandsidclaims- per-user
token_versionorauth_epoch - server-side denylist or session store for high-risk events
- immediate invalidation on role change, password reset, MFA reset, or suspected compromise
JWT validation example with explicit constraints
import { jwtVerify, createRemoteJWKSet } from "jose";
const JWKS = createRemoteJWKSet(new URL("https://idp.example.com/.well-known/jwks.json"));
export async function verifyAccessToken(token: string) {
const { payload } = await jwtVerify(token, JWKS, {
issuer: "https://idp.example.com/",
audience: "saas-api",
algorithms: ["RS256"],
clockTolerance: "5s"
});
if (!payload.jti || !payload.sid || !payload.sub) {
throw new Error("Missing required claims");
}
return payload;
}Notice what this does not do: it does not blindly trust any signed JWT forever.
4. Storing tokens where the wrong component can read them
For browser-based SaaS, this remains one of the highest-impact design decisions.
If the browser must hold sensitive tokens in localStorage, any meaningful XSS issue becomes far more dangerous. That is one reason many teams move toward a backend-for-frontend pattern, where the browser gets an HttpOnly secure cookie and the backend handles token exchange with the IdP.
Better defaults:
- Prefer
HttpOnlysecure cookies for browser sessions. - Keep access tokens short-lived.
- Avoid long-lived bearer tokens in JavaScript-accessible storage.
- Do not put tokens in URLs, query strings, or fragments that may be logged or copied.
- Do not expose raw refresh tokens to frontend code unless you have a strong reason and strong controls.
5. Broad cookie scope and weak session boundaries
A cookie scoped too broadly can be read or overwritten across sibling subdomains, staging environments, or legacy hosts you forgot were still alive.
Teams often protect the primary app and forget the wider cookie boundary.
Review:
- domain scope
- path scope
- secure flag
HttpOnlySameSite- staging vs production isolation
- subdomain trust assumptions
Weak boundaries make session hijacking prevention much harder than it should be.
6. Missing kill switches for real-world security events
When one of these happens, old sessions should not quietly survive:
- password change
- MFA reset
- role downgrade
- team removal
- account suspension
- device reported lost
- impossible-travel or risk spike
- refresh token reuse
- admin “log out all sessions”
If the session layer is not event-aware, incident response becomes slower and attackers keep time on target longer than they should.
Replay and theft paths engineering teams still underestimate
Attackers do not only steal tokens through “obvious” compromise.
Common real-world paths include:
- XSS reading tokens from browser storage
- session fixation before login
- verbose logs or APM traces capturing bearer tokens
- tokens exposed in support screenshots or browser sync data
- mobile debug builds and local backups
- refresh endpoints with no CSRF protection in cookie-based flows
- stale sessions after password reset or role change
- shared devices retaining trusted session state
- analytics or error tooling that accidentally captures auth artifacts
That is why session token security should be threat-modeled across frontend, backend, API gateway, support tooling, logging pipelines, and incident response—not just at the IdP boundary.
Minimal event schema for session telemetry
{
"event": "token.refresh",
"user_id": "u_123",
"session_id": "s_abc",
"jti": "jti_789",
"family_id": "fam_456",
"rotated_from_jti": "jti_555",
"ip": "203.0.113.10",
"ua_hash": "6e1c...",
"result": "success",
"risk_score": 41
}Do not log raw tokens. Log identifiers, outcomes, and context.
Simple reuse-detection query idea
SELECT family_id, COUNT(*) AS refresh_events
FROM auth_refresh_events
WHERE reuse_detected = true
AND event_time >= NOW() - INTERVAL '24 hours'
GROUP BY family_id
ORDER BY refresh_events DESC;Website Vulnerability Scanner tool by Pentest Testing Corp
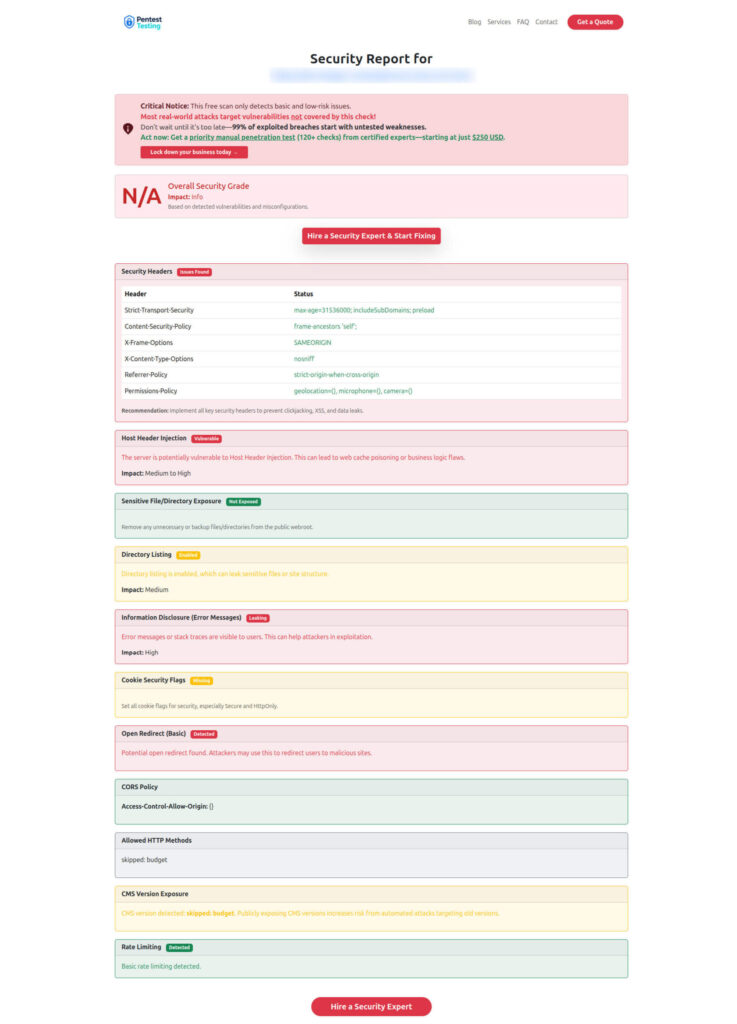
A fast baseline check is still useful before you move into deeper authenticated testing. Our Free Website Vulnerability Scanner is a practical first-pass check for public-facing issues such as HTTP security headers, exposed sensitive files, weak cookie settings, open redirects, CORS issues, and information leakage. Use it to catch obvious hygiene gaps early, but do not mistake it for a full session token security assessment.
Secure lifecycle patterns for session token security
Here is a practical baseline for modern SaaS teams.
Issue trust in layers
A useful model is:
- short-lived access token: 5–15 minutes
- rotating refresh token: 7–30 days depending on risk
- per-device session record on the backend
- absolute session lifetime plus idle timeout
- step-up authentication for high-risk actions
Examples of high-risk actions:
- billing changes
- API key generation
- export/download of sensitive data
- admin role changes
- MFA reset
- account recovery updates
Separate identity proof from ongoing authorization
Initial authentication proves who the user is. It does not guarantee every later request deserves the same trust level.
Use risk signals during the session too:
- device change
- IP anomaly
- geo jump
- unusual API sequence
- access to unusually sensitive resources
- refresh from a new browser fingerprint
- repeated failed refresh or reuse attempts
Keep revocation server-aware
Purely stateless trust is attractive until you need to contain an incident quickly.
If your app cannot answer “Which sessions are active for this user right now?” or “Can I kill only the compromised device without logging out everything?” then your session model is probably too thin.
Good systems can:
- show active sessions
- revoke one session or all sessions
- revoke by device
- revoke by token family
- revoke by risk event
- invalidate after policy or entitlement change
Hash refresh tokens at rest
Treat refresh tokens more like passwords than like harmless metadata.
Store only a hash server-side. If your session store leaks, you do not want attackers to immediately replay valid raw refresh tokens.
Use cache and response controls carefully
Auth responses, token exchanges, and sensitive session endpoints should not be accidentally cached by browsers, proxies, or CDNs.
Use appropriate Cache-Control and Pragma headers, and review intermediary behavior in staging and production.
Prefer safer browser patterns
For browser SaaS specifically:
- prefer
HttpOnlycookies over frontend-readable bearer storage where possible - scope cookies narrowly
- choose
SameSiteintentionally - protect state-changing endpoints against CSRF
- consider a backend-for-frontend design if your current SPA stores too much trust in the browser
How to test session token security controls
Scanners rarely catch the most important session flaws because these issues are stateful and workflow-driven.
That means manual testing matters.
A good session token security test plan should include:
- session fixation checks before and after login
- token rotation after login and privilege change
- refresh token replay after rotation
- reuse detection and family invalidation
- logout invalidation across browser tabs and devices
- password reset invalidation
- role change invalidation
- session survival after account disable or entitlement removal
- CSRF testing for refresh/logout/state-changing flows
- cookie scope and flag review
- token leakage into logs, URLs, telemetry, and support workflows
- BFF vs SPA storage review
- rate-limit and abuse review on refresh endpoints
Benign validation example: does logout really invalidate the session?
# 1) authenticate and store cookies
curl -i -c cookies.txt -X POST https://app.example.com/login \
-H "Content-Type: application/json" \
-d '{"email":"[email protected]","password":"REDACTED"}'
# 2) call an authenticated endpoint
curl -i -b cookies.txt https://app.example.com/api/me
# 3) log out
curl -i -b cookies.txt -X POST https://app.example.com/logout
# 4) try to reuse the old session
curl -i -b cookies.txt https://app.example.com/api/meExpected result: the final request should fail cleanly.
Benign validation example: old refresh token reuse
# Token A is used once to obtain Token B.
# Replay Token A again and verify:
# - it fails
# - the refresh family is flagged or revoked
# - alerting is generated if policy requires itIf your application passes one-token-at-a-time validation but fails sequence-based testing, you still have a real problem.
Sample report by our tool to check Website Vulnerability
Related Reading
If you want to go deeper into adjacent authentication, token abuse, and post-login security patterns, these Cyber Rely articles are strong companion reads:
- OAuth Consent Phishing Prevention for SaaS Teams — useful as the closest companion piece, because it covers how attackers gain durable access through OAuth approvals before weak session handling makes containment harder.
- Stop OAuth Abuse Fast with 7 Powerful Controls — a practical follow-on for token abuse, consent phishing, grant review, and revocation workflows across SaaS environments.
- 7 Best Ways to Stop Session Replay Attack in React.js — relevant for frontend teams working on browser-side token exposure, secure cookies, CSP, redaction, and session-handling risks in modern SPAs.
- 5 Proven CI Gates for API Security: OPA Rules You Can Ship — a strong fit for engineering teams that want to shift authentication and token-control validation earlier into CI/CD instead of relying only on production review.
- 7 Powerful Forensics-Ready Telemetry Patterns — useful for the sections on logging, token misuse detection, incident reconstruction, and proving what happened after a suspicious session event.
- 9 Powerful Forensics-Ready APIs for Microservices — a good companion for backend teams that need better traceability across identity, session, and service-to-service calls in distributed SaaS systems.
Where Cyber Rely fits your Security requirements
- Cybersecurity Services
- API Penetration Testing Services
- Network Penetration Testing Services
- Schedule a Free Consultation
Final takeaway
The biggest session token security failures usually do not come from exotic crypto mistakes.
They come from ordinary design shortcuts:
- trust that lasts too long
- tokens that cannot be revoked
- sessions that never rotate
- refresh flows that accept replay
- storage choices that make token theft easier than it needs to be
- logging and recovery workflows that quietly leak trust artifacts
If login is where identity begins, the session layer is where real application trust lives.
That is the layer worth testing like an attacker and designing like an incident responder.
Validate authentication and session flows through targeted security testing and engineering review. Start with our API Penetration Testing Services, or schedule a free consultation to review session fixation, refresh-token replay, token revocation, and post-login abuse paths in your environment. You can also use the Website Vulnerability Scanner as a fast first-pass baseline before deeper authenticated testing.
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about Session Token Security.